Internet of Doom: The Security Vulnerabilities of Connected Devices
Join the DZone community and get the full member experience.
Join For FreeSecurity in the Internet of Things is a fairly common concern these days - you know, Heartbleed, toasters, that kind of thing - but you may not even have considered the greatest threat to your connected devices: classic 1990s first person shooters.
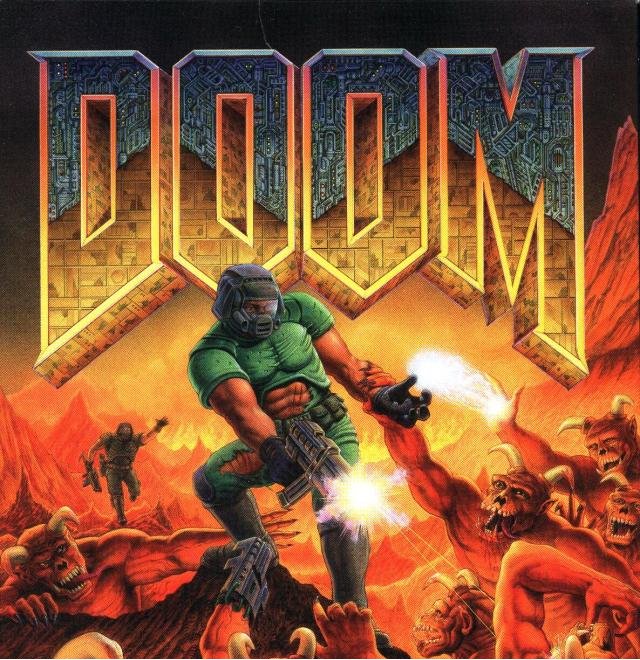
That's the scenario presented in this recent experiment from Context Information Security. By taking advantage of a web interface that require no user authentication, the Context team managed to get Doom up and running on a Canon Pixma printer. Obviously Doom is not the point in itself, so much as an illustration of the vulnerability, but it definitely gets the idea across. According to Michael Jordon at Context, the vulnerability was fairly serious:
At first glance the functionality seems to be relatively benign, you could print out hundreds of test pages and use up all the ink and paper, so what? The issue is with the firmware update process. While you can trigger a firmware update you can also change the web proxy settings and the DNS server. If you can change these then you can redirect where the printer goes to check for a new firmware. So what protection does Canon use to prevent a malicious person from providing a malicious firmware? In a nutshell - nothing...
Jordon's post goes into detail on how the encryption was broken. Canon was contacted and informed of the problem, and responded that it would be fixed, but Jordon warns that it's not a unique scenario. While this particular technique is not currently a common concern, it demonstrates the reality of security concerns when it comes to IoT devices. Once everything is connected, how many devices will be vulnerable? How confident can we be that the creators of these devices will be cognizant of these issues?
As a potential catch-all solution, Context offers a strange bit of advice:
Context recommends that you do not put your wireless printers on the Internet, or any other ‘Internet of Things’ device.
So, there you go - one way to be sure. The Internet of Things can't help but be secure if you get rid of that whole "Internet" part.
Opinions expressed by DZone contributors are their own.

Comments